Cybersecurity Solutions
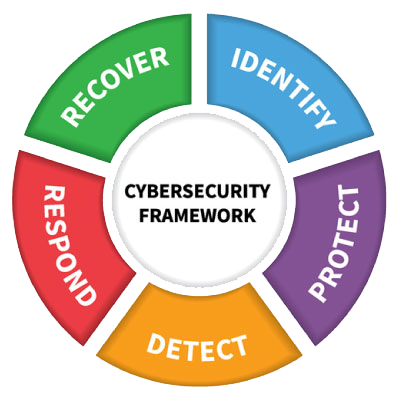
SWK TECHNOLOGIES’ CYBER THREAT PROTECTION SERVICES ARE A COLLECTION OF SOLUTIONS THAT ARE DESIGNED TO MEET THE NEEDS FOR A VARIETY OF CYBER THREATS.

The changing threat landscape has increased risk and made it difficult for small businesses to keep up. Today’s threats are stealthier and more complex than ever. Cybercriminals only need to find a single weakness to exploit and will use any means necessary to find vulnerabilities.
Dealing with and recovering from a security incident is extremely costly. SWK Network Services provides a variety of solutions to provide your network with the proactive and preventative defenses to keep you safe.
Advanced Endpoint Protection (Enhanced Cybersecurity)
24×7 Security Operations Center (SOC) – The SOC will provide 24×7 monitoring and alerting. For Critical alerts, the SOC will take action to isolate and remediate the threats. Using the endpoint protection technology, the SOC can identify and confirm malicious attacks in progress and, when discovered, will activate remediation steps including scrubbing the system of any remnants of the attack such as processes or registry keys created. In more extreme cases such as ransomware, the SOC will roll back the system to restore system and data access.
Unified Security Event Manager (Advanced Cybersecurity Data and Analysis)
Using security information and event management (SIEM) technology, data is collected, analyzed, and correlated from network devices, endpoint logs, and threat intelligence feeds. This information is used to identify security incidents, policy violations, fraudulent activity, and other threats. When such activities are identified and validated, the SOC will mitigate the attack while providing advanced remediation documentation and next steps. SWK will engage with the Customer per defined Incident Response Procedures to apply a permanent fix.

Multi-factor Authentication
With hackers and scammers lurking around every corner of the internet, you need the ability to confidently and securely log into all your devices and accounts. Multi-Factor Authentication (MFA) offers the easiest solution to this problem, granting you the certainty that a cyber criminal won’t be able to log into your account with just your password. MFA sets up a wall of defense, requiring multiple steps to access an account, think of it as one door with two separate locks that require two separate keys you can’t get in if you found just one.
Security Awareness Training
Did you know…91% of successful data breaches start with a phishing attack
Training your employees is the best defense against today’s sophisticated phishing and ransomware attacks. More than ever, employees are the weak link in an organization’s network security. They are frequently exposed to sophisticated phishing and ransomware attacks. Employees need to be trained and remain on their toes with security top of mind.
We offer the world’s most popular integrated platform for security awareness training combined with simulated phishing attacks. Find out how we can help you manage the continuing problem of social engineering and create a human firewall.

Dark Web Monitoring
Our service is designed to help both public and private sector organizations detect and mitigate cyber threats that leverage stolen email addresses and passwords. We leverage a combination of human and artificial intelligence that scours botnets, criminal chat rooms, blogs, Websites and bulletin boards, Peer to Peer networks, forums, private networks, and other black-market sites 24/7, 365 days a year to identify stolen credentials and other personally identifiable information (PII).
Simply Secure Encryption
PCs are still the heart and soul of employee productivity.
There’s more data here for thieves than any other mobile device. Additionally, industry, national, state and local regulations require encryption of all at risk consumer data. Still, many businesses fail to comply, leaving customers and employees vulnerable to identity theft, opening the possibility for legal problems, and allowing sensitive corporate information to escape.
Leveraging on-board encryption tools from Microsoft, SWK’s Simply Secure Encryption allows us to enforce and manage workstation encryption from the cloud while being completely transparent to the user.
Vulnerability Testing
Network security regulations are increasingly becoming stricter and more comprehensive in response to the growing rate of breaches targeting organizations holding personal data. SWK’s Network Vulnerability Testing also provides a tool for achieving data privacy compliance by allowing you to conduct regular vulnerability testing of your system. This examination enables you to review the effectiveness your cybersecurity practices and demonstrate compliance to regulatory agencies.
Our test will map and scan up to five (5) public IP addresses on your network to determine if they are vulnerable to the latest threats. We’ll provide you with a report detailing our findings, then we’ll schedule a call to discuss your environment and recommend potential remedies.